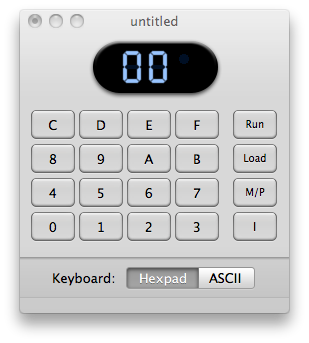
I’ve been tinkering some more in chapter 3 of Tom Pittman’s Short Course in Programming. I still think the book is excellent but some of the concepts are starting to become a bit confusing. For instance, when you take input from the hex keypad via the 6C INP 4 command, the next byte after that one gets modified if your memory protect is not enabled. It seems this could make input sanitization a difficult task. It also can make programs run unpredictably if you get a byte or two misplaced. Of course that is the pitfall with assembly language in the first place. To explain what I mean, enter in this program:
0000 3F BN 4 Wait for you to press I
0001 00 3F branches to THIS address if you don’t press “I”, if you do press “I”, it skips to the next address
0002 6c INP 4 Take whatever is in the IN 4 buffer and put it into the next location in memory
0003 00 IDL It actually doesn’t matter WHAT you put in this spot since the 6C command will change it anyways
0004 00 IDL after it 6C changes the previous bit, stop (or not depending on what input you send to the program)
Now run the program and type in 6C and press the “I”. I hope you are watching the memory contents window now because that’s crazy. Re-enter the program and experiment with some other values.
I have absorbed a few other interesting things too. First one that I like is the C4 NOP command. No op simply skips to the next byte. This is good for when you delete a command from memory but you don’t have enough room for a 30 BR LOOP followed by an address byte.
Next thing I like is the 64 OUT 4 command. That command outputs to the hex display whatever is in the byte following the command. For instance:
0000 64 OUT 4 This outputs the next byte to the display
0001 FF This will be output to the display
0002 00 IDL Idle until further instructed
There are also other output lines but as far as I can tell, they are attached to anything in the emulator.